
Terrorism National Terrorism Advisory System - Current Status:
|
||||||
Background
As with other aspects of the CERT program it is clear that the professional services, in this case law enforcement, will not be able to handle all contingencies and it is up to the community to provide support in the anti-terrorism struggle. "No one knows the community better than the community itself"In an effort to include the community in this aspect of law enforcement, New York City Police Department introduced its "Shield" program - "Counter Terrorism through Information Sharing", described here. Based on this program a number of liaison officers have been trained to, in turn, train the community. This is known as the "Terrorism Awareness" Community Outreach Program. The goal countrywide is to train 20,000 people a year to be "the eyes and ears of law enforcement". As of the Spring of 2009 community training courses are beginning to be held in the South Bay area. As more information about the program becomes available we will provide more details. For the time being the following sections give a few pointers of what community members can do to aid the authorities. Watch the News & Events page for information on training courses available to Lomita residents. The Seven Signs of Terrorism1. SurveillanceThe first sign is someone trying to monitor or record activities. If terrorists are targeting a specific area they will most likely be observed in that area during the planning phase of the operation. Terrorists will attempt to determine the strengths, weaknesses, and number of personnel that may respond to an incident. Routes to and from the target are usually established during the surveillance phase. It is important to note suspicious actions such as someone using cameras (still or video), drawing diagrams or annotating on maps, using vision-enhancing devices, and being in possession of floor plans or blueprints of places such as hightech firms, financial institutions, or government/military facilities. Any of these surveillance type acts MAY be an indicator that something is not right and should be reported immediately. Nothing is too insignificant. 2. Elicitation/ Seeking InformationThe second sign is the attempt to gain information through inquiries. This includes anyone attempting to gain information about a place, person or operation. Elicitation attempts can be made by mail, fax, telephone, or in person. Examples would be someone inquiring about a critical infrastructure like a power plant, water reservoir or a maritime port. Terrorists may attempt to research bridge and tunnel usage, make unusual inquiries concerning shipments, look into how a facility such as a hospital operates, attempt to obtain building plans or blueprints or make repeated requests to tour government or other facilities. They may also attempt to place “key” people in sensitive work locations to gain intelligence. 3. Tests of SecurityTests of security or probing are techniques terrorists would use to attempt to gather data. These are usually conducted by driving past or even penetrating the target, moving into sensitive areas, and observing security or law enforcement response. Specific areas of interest to terrorists would include how long it takes security or law enforcement to respond to an incident, number of responding personnel, or the routes taken to a specific location. Terrorists may also try to penetrate physical security barriers or test the response procedures in order to assess strengths and weaknesses. Vehicles may be parked for unusually long periods of time, sometimes in no parking areas, as a test of security. 4. Acquiring SuppliesThis may be a case where someone is purchasing or stealing explosives, weapons or ammunition. It could be the unusual purchasing or storing of fertilizer or harmful chemicals. Terrorists would also find it useful to acquire law enforcement equipment and identification, military uniforms and decals, as well as flight passes, badges or even flight manuals. Terrorists often use false or stolen identification documents including passports and driver licenses. They may try to produce counterfeit identification by photocopying. Any of these items would make it easier to gain entrance to secured or usually prohibited areas. Anyone wearing a uniform should have the proper identification on them. 5. Suspicious People Who Do Not BelongAnother pre-incident indicator is observing suspicious people who just don’t belong. This includes suspicious border crossings, stowaways aboard a ship or people jumping ship in a port. It could be someone in a workplace, building, neighborhood or business establishment who does not fit in because of their demeanor or unusual questions he/she is asking, or statements they make or because their clothing does not blend with the surrounding environment. This does not mean we should profile individuals, but it does mean we should profile behaviors. 6. Dry Run/Trial RunAnother sign to watch is for “dry runs.” Before the execution of the final operation or plan, a practice session will be run to work out the flaws and unanticipated problems. This is especially true when planning a kidnapping but it can also pertain to bombings. A dry run may be the heart of the planning stage of a terrorist act. If you find someone monitoring a police radio frequency and recording emergency response times, you may be observing a dry run. Multiple dry runs may be conducted at or near the target to gain intelligence. 7. Deploying Assets/Getting Into PositionThe seventh and final sign to look for is someone deploying assets or getting into position. This is your last chance to alert authorities before the terrorist act occurs. It is also important to remember that pre-incident indicators may come months or even years apart. Therefore, it is extremely important to document every fragment of information, no matter how insignificant it may appear, and forward this information to the authorities. Videos going over these points in more detail can be found here , here, and here. Early Warning SignsBehavior:
Criminal Activity:
Equipment
Surveillance
The Five "W"'sWhat to Remember When Reporting Suspicious Activity:
Although it is widely perceived that the terrorist threat comes from people of middle eastern origin, this preconception is counter productive. It is important to focus on the behavior and not the race or religion of anyone you may suspect of terrorist activity. On the other hand it is also important not to let political correctness prevent you from reporting what you honestly believe to be suspicious behavior. Accounts of witnesses to crimes and accidents have proved to be notoriously unreliable. The same is likely to be true in reporting suspect terrorist activity. To help focus on the important aspects of a potentially suspicious incident we have included an Incident Report Form which itemizes the important details to try to remember and note as soon as possible. Who to Report ToMany communities are assigning a "Terrorism Liaison Officer" who is the focal point for potential terrorist activity. In the case of Lomita please contact 911 if you see activity which is of a truly suspicious nature. Useful Links
|

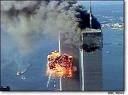 As the horrific events of September 11, 2001 recede into the past it is easy to become complacent about the threat of terrorism. Yet experts agree that the threat remains very real. While most would acknowledge that our community is probably low on the list of possible targets for a major terrorist attack, the Greater Los Angeles area could well be a prime target for such an outrage. Furthermore since terrorist attacks often take a considerable amount of planning, would-be terrorists could well hang out in quiet communities such as Lomita. Hence vigilance is the keyword.
As the horrific events of September 11, 2001 recede into the past it is easy to become complacent about the threat of terrorism. Yet experts agree that the threat remains very real. While most would acknowledge that our community is probably low on the list of possible targets for a major terrorist attack, the Greater Los Angeles area could well be a prime target for such an outrage. Furthermore since terrorist attacks often take a considerable amount of planning, would-be terrorists could well hang out in quiet communities such as Lomita. Hence vigilance is the keyword.